Power Up Your Network Security
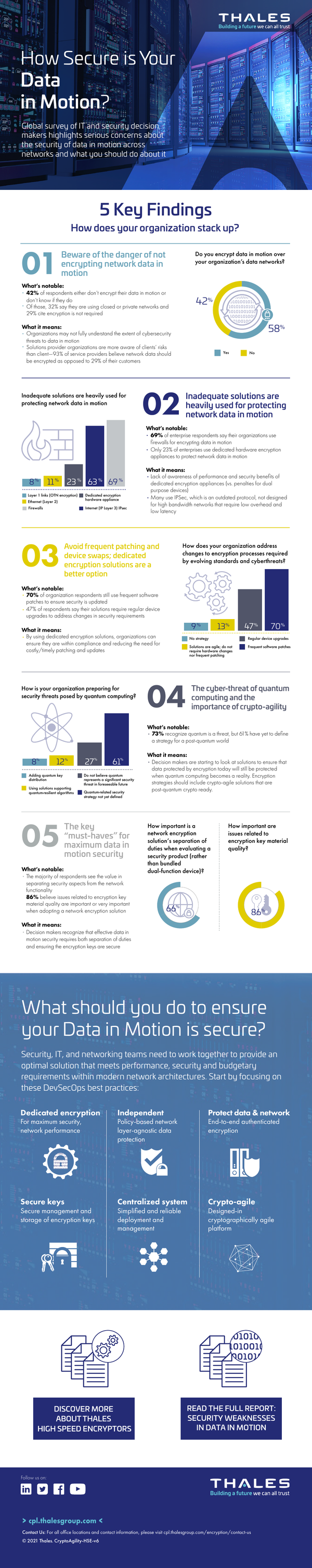
Data is in its most vulnerable state when in transit. As cybercriminals are increasingly sophisticated, it’s critically important to bolster your data-in-motion security now to ensure your data privacy and security posture are way ahead of the increasing threat landscape.
SureDrop
Secure file sharing and collaboration
Share, sync and store files in the cloud or on-premises securely with an enterprise-class, end-to –end security solution.
Thales SureDrop is designed for organizations with strong security policies around file sharing, synchronization and storage, but still need the productivity benefits of a fully-featured file sharing solution.
Key Features:
- SureDrop leverages Data Protection on Demand (DPoD) Luna Cloud HSM services for a secure root of trust.
- Enabling Microsoft Active Directory controls, SureDrop can be easily integrated into Microsoft Office and 365 for a seamless user experience.
- Maximum encryption key security and key management, based on seamless integration with Thales CipherTrust platform.
- SureDrop can also be integrated into SafeNet Trusted Access for multi-factor authentication.
Sign up now for a free 90-day evaluation of SureDrop
IDM DACH 2024
Discover the leading innovations shaping CIAM
7 MARCH 2024 | FRANKFURT
Mar 7, 2024 00:00:00
Days43
Hours09
Minutes33
Seconds41
2023 Year in Recap
Thales Identity and Access Management
Visit Thales OneWelcome at Gartner Identity & Access Management Summit
4-5 March, 2024 | London, UK
Visit Thales OneWelcome at
Gartner Identity & Access
Management Summit
4-5 March, 2024 | London, UK
Daily challenges like ransomware, data sprawl, insider threats and regulatory violations, are often tackled with unconnected, siloed tools. This increases risks, complexities, and total cost of ownership.
With that, our mission is clear: to provide you with complete visibility and control over your sensitive data and all paths to it, securing it confidently from its creation and across its lifecycle.
Trusted Security
- End-to-end, standards-based encryption
- Robust audit capabilities
- On-Premises version for organizations with higher security standards
- Advanced encrypted file fragmentation and storage
Intuitive and Easy to Use
- Supports multiple devices, including mobile. Microsoft Office and 365 compatible
- Intuitive user interface, based on angular framework
- Simple user enrollment and setup in minutes. Microsoft Azure Active Directory compatible
A winning combination for customers
Listen to Sebastien Cano, SVP, Thales Cloud Protection & Licensing, as he shares exclusive insights into the added benefits Thales can offer you.
BOOK A MEETINGA winning combination for customers
Listen to Sebastien Cano, SVP, Thales Cloud Protection & Licensing, as he shares exclusive insights into the added benefits Thales can offer you.
BOOK A MEETINGA winning combination for customers
Listen to Sebastien Cano, SVP, Thales Cloud Protection & Licensing, as he shares exclusive insights into the added benefits Thales can offer you.
BOOK A MEETINGA winning combination for customers
Listen to Sebastien Cano, SVP, Thales Cloud Protection & Licensing, as he shares exclusive insights into the added benefits Thales can offer you.
BOOK A MEETINGAgenda
| Table Header | Table Header |
|---|---|
| 09:00 - 10:00 | Name of the event Lorem ipsum dolor sit amet, consectetur adipiscing elit. |
| 10:00 - 11:00 | Name of the event Lorem ipsum dolor sit amet, consectetur adipiscing elit. |
Venue

QEII Centre, London
The Queen Elizabeth II Centre (QEII Centre) is a conference facility located in the City of Westminster, London, close to the Houses of Parliament, Westminster Abbey, Central Hall Westminster and Parliament Square.
Address: Broad Sanctuary, London SW1P 3EE, United Kingdom
Watch the video!
This 1-minute video shows why Thales High Speed Encryptors (HSE) are far superior to IPSEC tunnels. Make better security, better performance, and easy setup and management.
Why Thales?
Security Expertise
Thales excels in robust network security
Performance
Rapid encryption without compromising data transfer
Compliance
Meets strict regulations for data protection
Leading a new era in cybersecurity with a combined product portfolio
Versatility
Crypto-Agile solutions for diverse security needs
Key Management
Advanced handling of cryptographic key security
Integration Capabilities
Seamless integration with existing IT ecosystems
Leading a new era in cybersecurity with a combined product portfolio
Application Security
We protect modern and hybrid applications against advanced and multi-vector attacks regardless of where they are running.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Application Security
We protect modern and hybrid applications against advanced and multi-vector attacks regardless of where they are running.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Application Security
We protect modern and hybrid applications against advanced and multi-vector attacks regardless of where they are running.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Application Security
We protect modern and hybrid applications against advanced and multi-vector attacks regardless of where they are running.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Identity Proofing
Ensure online users are who they claim to be, and protect against identity fraud.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Identity Proofing
Ensure online users are who they claim to be, and protect against identity fraud.
BOOK A MEETINGIdentity & Access Management
Seamless, secure and trusted access online for customers, employees and partners.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Data Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGLeading a new era in cybersecurity with a combined product portfolio
Data Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGData Security
We redefine how sensitive data is secured from knowing where it is, who has access to it, and when abuse occurs in real-time, to protecting it in all environments whether at rest, in motion, or in use.
BOOK A MEETINGTwo award-winning leaders join forces

Thales Wins Google Cloud Technology Partner of the Year Security
BOOK A MEETING
Imperva Named an API Security & Management Overall Leader
BOOK A MEETING
Data Protection on Demand Wins Cybersecurity Excellence Award
BOOK A MEETINGDiscover More
Protecting Your Data, Every Step of the Way.
Our Venue
Our impact in numbers
80M+
People rely on Thales to manage their digital identities
30,000+
Customers worldwide are being protected by Thales
750+
Engineers are innovating and enhancing our product offerings
A good and solid solution in constant evolution: We’ve been using the Thales OneWelcome Identity Platform to offer 1.3 million customers a simple and secure connection to our websites and mobile application since December 2020."
—Our customer at Gartner®
A year of successfully pushing boundaries
This year was a testament to our commitment to innovation, resilience and redefining what’s possible. Not only did we expand our product offerings to reach a truly global market, we also continued to explore and embrace the challenge of simplifying digital complexities and streamlining user journeys.
- We’ve re-entered the Gartner® Magic Quadrant™, this time promoted to ‘Visionary’ by achieving above average scores in innovation and market-responsiveness.
- The Thales OneWelcome Identity Platform went global, empowering enterprises worldwide to orchestrate frictionless, secure and trusted digital user journeys.
- Our partner portal went global too. Users around the world can leverage the power of CIAM in enabling digital transformation and strengthening supply chain security.
- We partnered with Colombia’s SoyYo to introduce passwordless authentication capabilities, streamlining digital identity management.
- Our new SafeNet eToken Fusion series now blends FIDO and PKI for heightened security across cloud and web applications on any device.
- We launched the SafeNet ID Prime FIDO Bio Smart Card, which uses biometrics instead of passwords, to safeguard users against account takeover and phishing.
Mitigate the Latest Threats with Quantum-Ready Solutions
Impending NIST quantum algorithms need to be deployed quickly upon standardisation, meaning your encryption technology must be agile and adaptable. 73% of organisations recognise quantum as a threat, but 61% have yet to define a crypto-agile strategy for a post-quantum world.
Thales High Speed Encryptors are purpose-engineered for dedicated, high-assurance network data security, and can help your organisation to deploy a future-proof quantum-ready data-in-motion strategy.
Get the “Quantum Computing & Quantum-Safe Security” White Paper
Source: "Security Weaknesses in Data in Motion Identified in Cybersecurity Survey", Thales October 2022
Schedule a meeting
Get Started with Thales & Imperva Together
Speak to an expertHigh Speed Network Encryption

Certified FIPS 140-2 L3, Common Criteria, NATO, UC APL, Thales Network Encryptors are preferred by market leading financial institutions, telcos and other commercial organisations and governments in more than 35 countries. Proven to deliver max uptime in the most demanding, performance intensive environments. The solutions have near-zero latency and can operate in full-duplex mode at full line speed with flexible, vendor agnostic interoperability.

The market’s most comprehensive data security offering
Our consolidated offering covers the entire spectrum of your data security needs, including:
- real-time visibility into your data activity
- access permissions monitoring
- smart risk intelligence
- in-depth defense across your entire security stack

The market’s most comprehensive data security offering
Our consolidated offering covers the entire spectrum of your data security needs, including:
- real-time visibility into your data activity
- access permissions monitoring
- smart risk intelligence
- in-depth defense across your entire security stack

The market’s most comprehensive data security offering
Our consolidated offering covers the entire spectrum of your data security needs, including:
- real-time visibility into your data activity
- access permissions monitoring
- smart risk intelligence
- in-depth defense across your entire security stack

Quote, Lorem ipsum dolor sit amet, consectetur adipiscing elit. Vestibulum sed lectus et nunc."
—Full Name and Job Title

Swift deployment with a secure, scalable B2B IAM solution
Experience quick deployment in just a few weeks. Our purpose-built, cloud-based B2B IAM solution caters to all your B2B user groups, delivering unmatched security, scalability, and ease of use for seamless collaboration across your B2B ecosystem
Managing Identities and Access for your Business Ecosystem
The only true B2B IAM solution to streamline collaboration and enhance security
Access the InsightsThe Power of Effective B2B Identity Management
Establish seamless collaboration and a scalable B2B ecosystem
Get the ebookDelegation User Management
End-to-end delegated user management for any B2B use case
Get the solution briefEmbrace B2B Identity Management to Minimize Third Party Access Risks
Discover a new approach to addressing modern B2B and B2B2C IAM challenges
Watch on-demandRecursos
Lee más sobre nuestra garantía de ciberseguridad y experiencia en gestión de datos.
La pandemia de ciberataques a la industria farmacéutica
Logrando privacidad y protección de propiedad intelectual mientras se acelera la innovación.
Access the InsightsUn ancla de confianza en un mundo digital
Aborda las brechas en la seguridad de dispositivos médicos, reduce riesgos y crea una ventaja competitiva usando Módulos de Seguridad de Hardware (HSM).
Get the ebookProtege el Internet de las Cosas Médicas (IoMT)
Descubre cómo las empresas biotecnológicas pueden proteger los dispositivos IoMT y encontrar el equilibrio perfecto entre agilidad, resiliencia y seguridad.
Get the solution briefAgilidad en un mundo post-cuántico
Cómo asegurar la agilidad criptográfica en la era post-cuántica.
Watch on-demand